For RV325, need suggestions for teleworker VPN client software As a volunteer church techie I've just installed RV325 in a scenario matching the description of small business. I've achieved port-forwarding from the outside world to a dummy host that is not mission-critical. Cisco Meraki offers an exceptionally simple and easy to use teleworker solution. Completely managed from the cloud, the Z1 appliance is ideal for small offic. The Teleworker VPN Client feature minimizes the configuration requirements at remote locations by allowing the security appliance to work as a Cisco VPN hardware client to receive the security policies upon the VPN tunnel from a remote IPsec VPN server.
Configuring Teleworker VPN Client Group Policies
To be able to complete the configuration of a Teleworker VPN Client group policy, you must have the following information ready.
•IPsec VPN server’s IP address or hostname.
•IPsec VPN server’s group policy name.
•Pre-shared key or digital certificates for IKE authentication.
Note Up to 16 Teleworker VPN Client group policies can be configured on the security appliance. You can create multiple group polices to connect to different VPN servers but only one VPN connection can be active at a time.
1.Click VPN > Teleworker VPN Client.
2.To add a group policy, click Add.

Other Options: To edit an entry, click the Edit (pencil) icon. To delete an entry, click the Delete (x) icon. To delete multiple entries, check them and click Delete.
The Teleworker VPN Client - Add/Edit window opens.
3.In the Basic Settings tab, enter the following information:
•Description: Enter the name for the group policy.
•Server (Remote Address): Enter the IP address or domain name of the remote IPsec VPN server.
•Activate Connection on Startup: Click On to automatically initiate the VPN connection when the security appliance starts up, or click Off to disable it. Only one VPN connection can be active on startup.
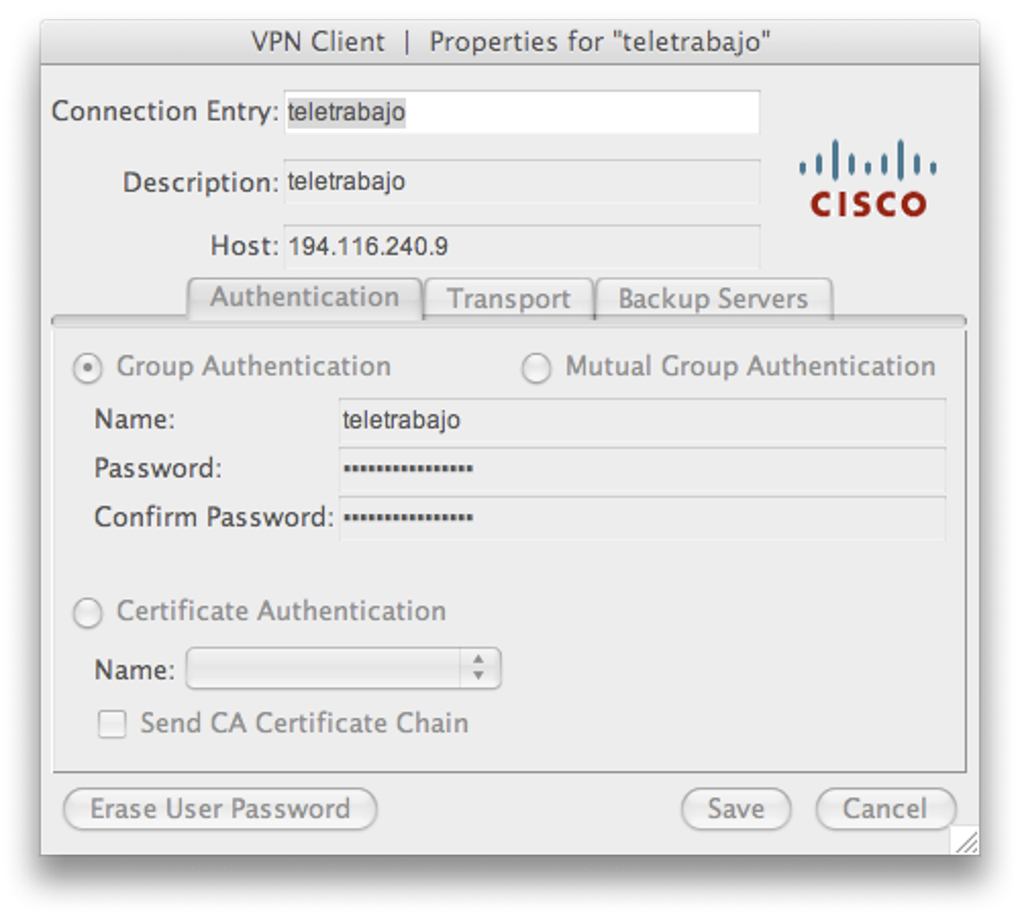
•IKE Authentication Method: The VPN client must be properly authenticated before it can access the remote network. Choose one of the following authentication methods:
–Pre-shared Key: Choose this option if the IPsec VPN server uses a simple, password-based key to authenticate and then enter the following information:
Group Name: Enter the name of the IPsec Remote Access group policy that is defined on the IPsec VPN server. The security appliance will use this group policy to establish the VPN connection with the IPsec VPN server. The IPsec VPN server pushes the security settings over the VPN tunnel to the security appliance.
Password: Enter the pre-shared key specified in the selected group policy to establish a VPN connection. The pre-shared key must be entered exactly the same here and on the IPsec VPN server.
–Certificate: Choose this option if the IPsec VPN server uses the digital certificate from a third party Certificate Authority (CA) to authenticate. Select a CA certificate as your local certificate from the Local Certificate drop-down list and select the CA certificate used on the remote IPsec VPN server as the remote certificate from the Peer Certificate drop-down list for authentication.
NOTE: You must have valid CA certificates imported on your security appliance before choosing this option. Go to the Device Management > Certificate Management page to import the CA certificates. See Managing Certificates for Authentication, page 350.
•Mode: The operation mode determines whether the inside hosts relative to the Cisco VPN hardware client are accessible from the corporate network over the VPN tunnel. Specifying an operation mode is mandatory before making a VPN connection because the Cisco VPN hardware client does not have a default mode. For more information about the operation mode, see Modes of Operation.
–Choose Client if you want the PCs and other devices on the security appliance’s inside networks to form a private network with private IP addresses. Network Address Translation (NAT) and Port Address Translation (PAT) will be used. Devices outside the LAN will not be able to ping devices on the LAN, or reach them directly.
–Choose NEM (Network Extension Mode) if you want the devices connected to the inside interfaces to have IP addresses that are routable and reachable by the destination network. The devices at both ends of the connection will form one logical network. PAT will be automatically disabled, allowing the PCs and hosts at both ends of the connection to have direct access to one another.
•VLAN: If you choose NEM, specify the VLAN that permits access from and to the private network of the IPsec VPN server.
•User Name: Enter the username used by the Teleworker VPN client to establish a VPN connection.
•User Password: Enter the password used by the Teleworker VPN client to establish a VPN connection.
4.In the Zone Access Control tab, you can control access from the zones in your network to the remote network if the Teleworker VPN client works in Client mode. Click Permit to permit access, or click Deny to deny access.
NOTE: The VPN firewall rules that are automatically generated by the zone access control settings will be added to the list of firewall rules with the priority higher than the default firewall rules, but lower than the custom firewall rules.
5.In the Advanced Settings tab, enter the following information.
•Backup Server 1/2/3: Enter the IP address or hostname for the backup server. You can specify up to three servers as backup. When the connection to the primary IPsec VPN server fails, the security appliance can initiate the VPN connection to the backup servers. The backup server 1 has the highest priority and the backup server 3 has the lowest priority.
NOTE: The Teleworker VPN client can get the backup servers from the IPsec VPN server during the tunnel negotiation. The backup servers specified on the IPsec VPN server have higher priority than the back servers specified on the Teleworker VPN client. When the primary connection fails, first try to connect to the backup servers specified on the IPsec VPN server, and then try to connect to the backup servers specified on the Teleworker VPN client.
•Peer Timeout: Enter the value of detection timeout in seconds. If no response and no traffic from the primary server or the backup server over the timeout, declare the peer dead. The default value is 120 seconds.
6.Click OK to save your settings.
7.A warning message appears saying “Do you want to make this connection active when the settings are saved? (Only one connection can be active at a time.)”
•If you want to immediately activate the connection after the settings are saved, click the Activate Connection button. When you create multiple Teleworker VPN Client group policies at a time, only one connection can be active after you save your settings. The security appliance will use the group policy that was last created or edited to initiate the VPN connection.
•If you only want to create the Teleworker VPN client group policy and do not want to immediately activate the connection after the settings are saved, click the Do Not Activate button. You can click the Connect icon to manually establish the VPN connection.
NOTE: This feature is different from the Active Connection on Startup feature. It is used to activate the connection immediately after the settings are saved, but the Activate Connection on Startup feature is used to activate the connection when the security appliance starts up.
8.Click Save to apply your settings.
Cisco Teleworker Vpn Client
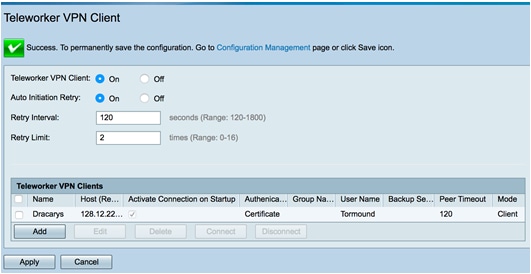
General Teleworker VPN Client Settings
This section describes how to enable the Teleworker VPN Client feature, configure the Auto Initiation Retry settings, and manually connect or disconnect the VPN connections.
1.Click VPN > Teleworker VPN Client.
2.Enter the following information:
•Teleworker VPN Client: Click On to enable the Teleworker VPN Client feature and hence set the security appliance as a Cisco VPN hardware client, or click Off to disable it.
NOTE: Enabling the Teleworker VPN Client feature will disable the Site-to-Site VPN and IPsec Remote Access features and terminate their connected VPN sessions.
•Auto Initiation Retry: Click On to enable the Auto Initiation Retry feature, or click Off to disable it.
When you enable Auto Initiation Retry, the security appliance (set as the Cisco VPN hardware client) first initiates the VPN connection to the primary server. If there is no response from the primary server after the timeout that you set in the Retry Interval field, the security appliance then re-initiates the VPN connection to the primary server. This continues for the number of times that you set in the Retry Limit field (or until the primary server is connected). If the primary server cannot be connected after the specified number of times, the security appliance tries to re-initiate the VPN connection to the backup servers by following the specified timeout and retry times. If all three backup servers cannot be connected, repeat the re-initiation process again and again until an IPsec VPN server can be connected.
When you disable Auto Initiation Retry, the security appliance first initiates the VPN connection to the primary server. If there is no response from the primary server in 120 seconds, the security appliance then re-initiates the VPN connection to the backup servers. If all three backup servers cannot be connected, repeat the re-initiation process again and again until an IPsec VPN server can be connected.
•Retry Interval: Specify how often, in seconds, that the security appliance re-initiates the VPN connection to the primary server and the back servers. The default value is 120 seconds.
•Retry Limit: Enter the number of times that the security appliance will retry a VPN connection initiation. The default value is 2.
3.Click Save to apply your settings.
4.To manually initiate the VPN connection, click the Connect icon in the Configure column. By default, the group policy that the Activate Connection on Startup setting is enabled will automatically initiate the VPN connection when the security appliance starts up. Only one VPN connection can be active at a time.
Comcast Teleworker Cisco

5.To manually terminate the VPN connection, click the Disconnect icon.
